If you think turning off your internet will keep you safe from ransomware, think again. Mamona ransomware has turned that simple safety tip upside down. This new malware can encrypt your files and lock you out—all without sending a single byte over the internet. For families, schools, businesses, and even government agencies, Mamona is a wake-up call. It reveals a major blind spot in how we think about cybersecurity, especially in places where sensitive computers are kept offline on purpose.

Traditional ransomware hits headlines every few months, with cybercriminals breaking into networks, stealing data, and demanding ransoms. But Mamona is different. It works in complete silence, needing nothing more than a USB stick and a few seconds to lock your digital life away. That makes it dangerous to everyone—not just big companies, but anyone who uses a Windows computer, plugs in a USB drive, or thinks “offline” means “safe.”
Table of Contents
Mamona Ransomware
| What is Mamona? | How Does It Spread? | Who’s at Risk? | How to Detect & Respond | Expert Insights |
|---|---|---|---|---|
| Offline ransomware; no internet, no external communication | USB drives, external hard disks, hidden files, autorun scripts | Windows users, especially in air-gapped/offline environments | Watch for .HAes extensions, README.HAes.txt files, rapid file changes, use advanced monitoring tools | Evades network detection, deletes itself, hard to trace |
Mamona ransomware has changed the game by proving that even the most secure, offline systems are not safe from modern cyber threats. Its ability to spread through simple USB sticks, encrypt files without internet access, and disappear without trace makes it a serious risk for everyone—families, schools, businesses, and governments alike.
The best defense is a combination of education, vigilance, and layered security. Limit physical device usage, monitor for unusual file changes, maintain regular offline backups, and keep all software up to date. For professionals, this means investing in advanced monitoring tools and fostering a culture where everyone is aware of cyber risks.
Cybersecurity is a team sport. From parents to presidents, everyone has a role in keeping our digital lives safe. The lessons from Mamona are clear: offline does not mean invulnerable, and simple habits—like being careful with USB drives—can make a huge difference.
What Exactly is Mamona Ransomware?
Mamona is a type of malicious software—what we call malware—that’s built to lock up your files and demand payment to unlock them. Instead of attacking over the internet like most ransomware, Mamona encrypts files using keys generated right on your own computer. It never “phones home” to a hacker’s server, never sends data out, and never receives instructions from the outside world. That makes it entirely offline, self-contained, and stealthy.
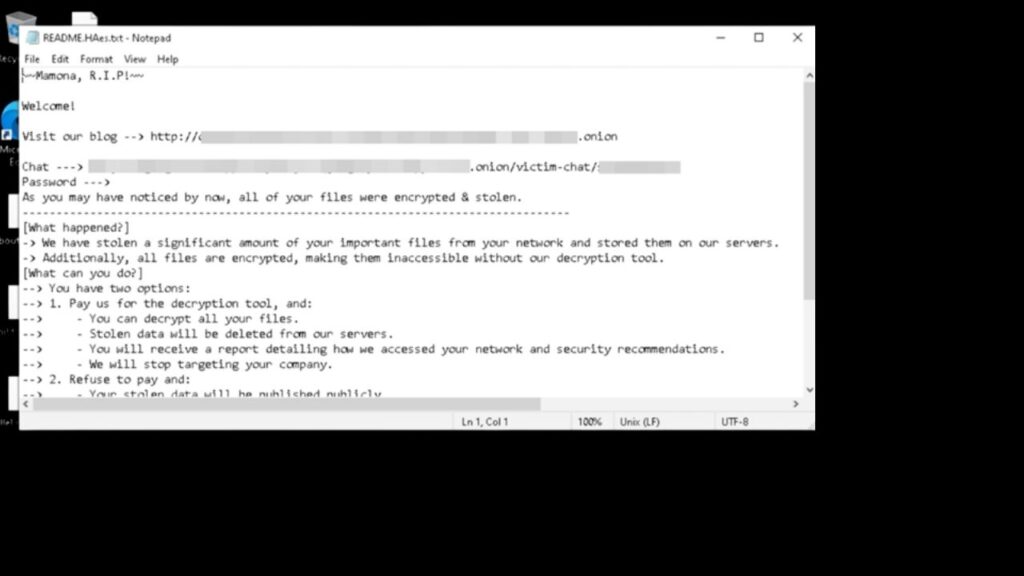
When you plug an infected USB drive into your computer, Mamona springs into action. It quickly encrypts your files, renames them with the .HAes extension, drops a ransom note called README.HAes.txt in multiple folders, and then—before you even notice—deletes itself to cover its tracks. The whole attack can be over in seconds, with almost no trace left behind.
This is a radical shift from what we’re used to. Most ransomware is loud: it shouts across the internet, steals files, and tries to make headlines. Mamona whispers, slips in through the back door, and leaves almost no evidence.
How Does Mamona Spread and Infect Computers?
Mamona’s favorite path is physical. It spreads through USB drives, external hard disks, memory cards, and other removable media. Someone plugs in a compromised device—maybe not even realizing it’s infected—and the malware quietly takes over. It doesn’t rely on email attachments, malicious downloads, or fake websites. It doesn’t need Wi-Fi, Ethernet, or Bluetooth. All it needs is physical access—and the simplest human habits.
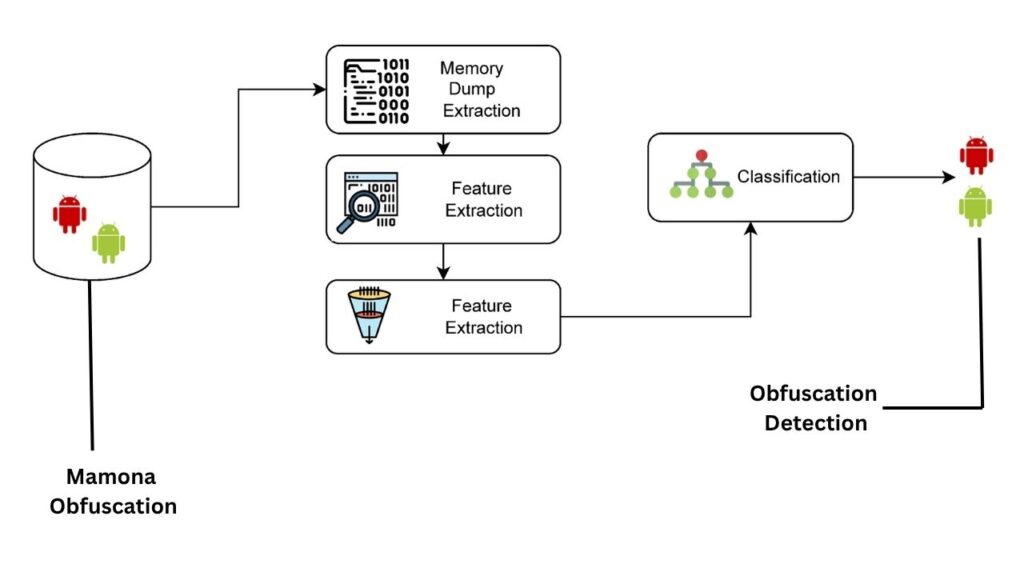
Once inside, Mamona uses obfuscation (hiding its true nature), hidden files, and autorun scripts to trick your computer into running it. Some versions abuse the Windows ping command (specifically, pinging the unusual address 127.0.0.7) to create a short delay, bypassing simple detection rules. Then, it encrypts your files with a custom-built algorithm, renames them with the .HAes extension, and drops its ransom note.
After the dirty work is done, Mamona deletes itself. It does this in a clever way: by spawning a separate command shell to erase its own file, making it almost impossible for standard security tools to catch it in the act.
Why Is This a Problem?
Mamona’s offline, self-sufficient, and fast nature creates several big problems:
- Air-gapped systems are not safe. These are systems kept offline to protect them from hackers. Mamona proves they can still be attacked if someone plugs in the wrong device.
- Detection is extremely difficult. Most security tools look for suspicious internet traffic or unusual network activity. Mamona generates none. It’s like a burglar who never makes noise.
- Forensic investigation is tough. Since the malware deletes itself, there’s often little left to analyze after an attack.
- Recovery is harder. Because encryption happens so quickly, backups are your best hope—but only if they are recent and offline.
- Anyone can use it. Mamona’s code is available as a “commodity” or “ready-made” toolkit, so even inexperienced criminals can deploy it.
Who Is Most at Risk from Mamona?
Almost anyone using Windows is at risk, but some groups are especially vulnerable:
- Businesses with critical, offline systems: Hospitals, power plants, government agencies, and labs often keep their most sensitive computers offline. Mamona proves this isn’t enough.
- Schools and families: Kids and employees frequently plug in USB drives without thinking. A single careless action can let Mamona in.
- Remote and hybrid workers: People who move between home and office, or who use USB drives to transport files, are easy targets.
- Organizations in Dehradun and across India: As digital adoption grows, so does the risk. Anywhere Windows is common, Mamona is a threat.
What Are the Signs of a Mamona Infection?
Detecting Mamona can be tricky, but there are clues:
- Files suddenly renamed with .HAes extensions (for example, document.docx becomes document.HAes)
- Ransom notes named README.HAes.txt appearing in multiple folders
- Strange, rapid changes to files—especially if your computer wasn’t doing anything unusual
- No unusual internet activity—because Mamona never calls out to the internet
If you see these signs, act fast. Disconnect the computer from any network, unplug any USB devices, and contact your IT or cybersecurity team immediately.
How Can You Protect Yourself, Your Family, and Your Organization?
Prevention is always better than cure. Here’s a step-by-step guide to staying safe from Mamona and similar threats, presented in plain, actionable language.
1. Limit USB and External Device Usage
- Disable autorun on all computers. This stops hidden scripts from running automatically when you plug in a USB drive.
- Only use trusted devices. Never plug in a USB drive, memory card, or external hard disk unless you know—and trust—exactly where it came from.
- Educate everyone. Teach kids, employees, and family members about the risks of unknown devices. It only takes one mistake to let malware in.
2. Monitor for Suspicious Activity
- Watch for new .HAes files. If you see files suddenly renamed this way, you may be infected.
- Check for ransom notes. Files named README.HAes.txt in multiple folders are a red flag.
- Monitor file changes. Use advanced tools (like Wazuh’s File Integrity Monitoring) to spot sudden, unexpected file modifications.
- Check for unusual commands. Tools that monitor system activity can help spot the abuse of the ping command or rapid self-deletion.
3. Backup Regularly—And Keep Backups Offline
- Back up important files often. Use external drives or cloud storage, but keep at least one backup completely offline (not connected to your main computer).
- Test your backups. Make sure you can restore files if needed. A backup that doesn’t work is no backup at all.
4. Use Security Software and Best Practices
- Keep your operating system updated. Always install the latest patches and security updates.
- Use antivirus and anti-malware tools. Even though Mamona is hard to detect, good security habits help against other threats.
- Limit user privileges. Don’t let everyone install software or change system settings.
- Implement endpoint detection and response (EDR). Advanced EDR platforms can spot suspicious activity even if there’s no network traffic.
5. Train Staff and Raise Awareness
- Regular training. Teach everyone—from the CEO to the newest intern—about basic cyber hygiene.
- Simulate attacks. Run drills to test how well your team responds to ransomware and other threats.
- Encourage reporting. Make it easy for people to report suspicious activity without fear of blame.
What Should Professionals Do Differently?
For IT and cybersecurity teams, Mamona requires a new approach:
- Focus on endpoint behavior. Because Mamona doesn’t use the network, network monitoring alone isn’t enough. Watch for rapid file encryption, new file extensions, and unusual system commands.
- Implement File Integrity Monitoring (FIM). Alert on unexpected file renames or encryption patterns.
- Deploy Endpoint Detection and Response (EDR). Advanced EDR can catch the subtle signs of Mamona’s activity, even without internet clues.
- Conduct regular security audits. Test your defenses with penetration testing and “red teaming” to find weak spots before criminals do.
- Patch and update relentlessly. Make sure every computer, server, and device is up to date with the latest security fixes.
What About the Cybercriminals Behind Mamona?
Mamona was originally developed by a cybercriminal using the alias “$$$”. Later, this same actor created a more advanced ransomware operation called GLOBAL GROUP, which targets not only Windows, but also Linux and macOS, and uses modern encryption techniques. GLOBAL GROUP is an example of how ransomware continues to evolve, but many of the lessons from Mamona still apply to these newer threats.
GPUHammer Exploit Targets NVIDIA GPUs, Threatens AI Model Integrity With Memory Flaw
FAQs About Mamona Ransomware
Q: Can Mamona spread through email or the internet?
A: No, Mamona spreads only through physical devices like USB drives. It does not use email or the internet to infect computers.
Q: Does paying the ransom guarantee I’ll get my files back?
A: There is no evidence that paying the ransom restores files. In fact, paying only encourages more attacks and funds further cybercrime.
Q: Are Mac or Linux computers safe from Mamona?
A: Mamona itself targets Windows systems, but related threats (like GLOBAL GROUP) can attack Linux and macOS. Always stay vigilant.
Q: How can I tell if my computer is infected?
A: Look for files renamed with .HAes extensions and ransom notes named README.HAes.txt. Sudden, unexplained file changes are a warning sign.
Q: Can antivirus software stop Mamona?
A: Traditional antivirus may struggle because Mamona is new, doesn’t communicate online, and deletes itself quickly. Advanced behavioral monitoring is more effective.
Q: What organizations are most at risk?
A: Any organization using Windows—especially those with critical, offline systems—faces risk. Schools, hospitals, businesses, and government agencies are all potential targets.
Q: Is there a patch or update to prevent Mamona?
A: There is no specific patch, but keeping your operating system and security software up to date is always a good defense.